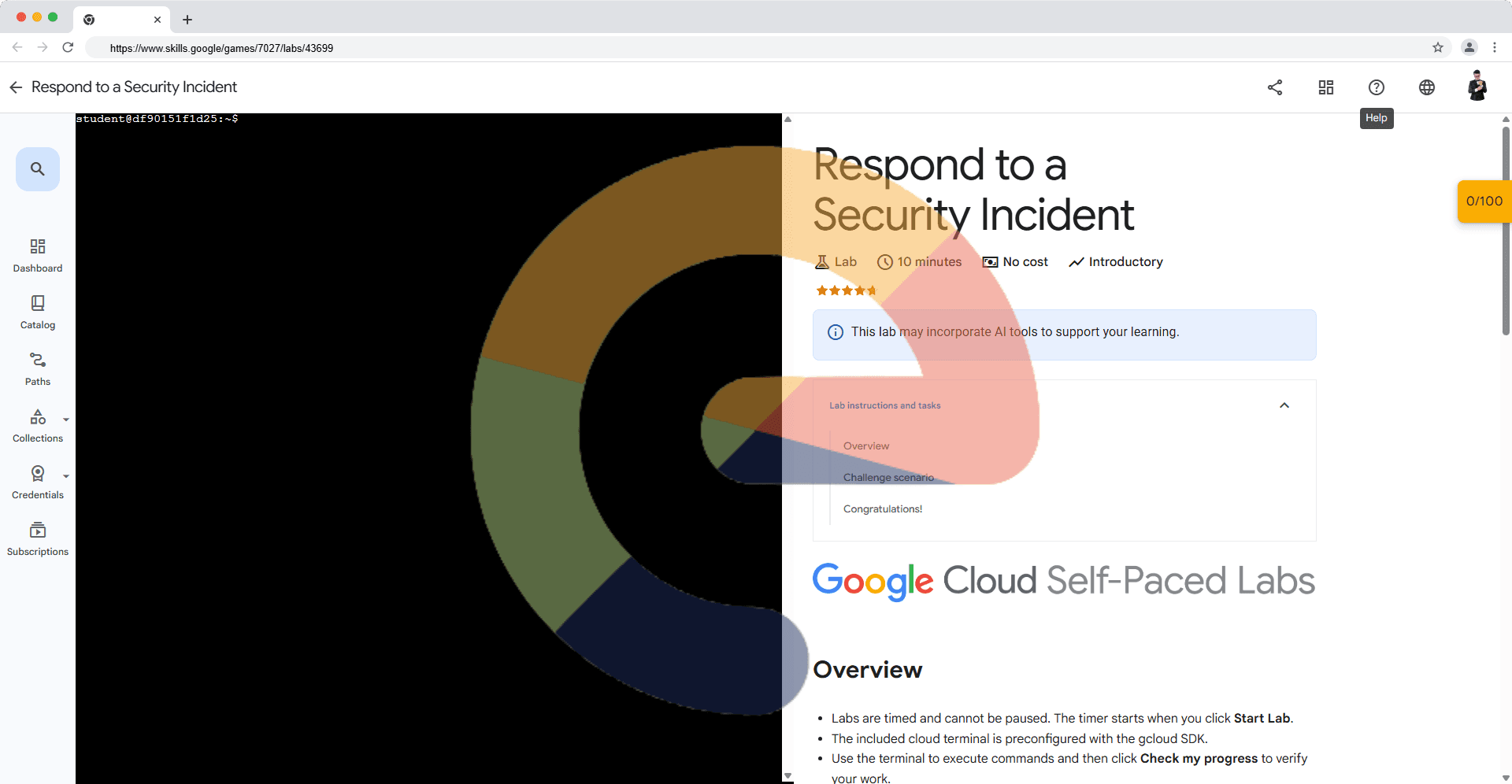
Respond to a Security Incident (Solution)
A passionate full-stack developer from @ePlus.DEV
Overview
Labs are timed and cannot be paused. The timer starts when you click Start Lab.
The included cloud terminal is preconfigured with the gcloud SDK.
Use the terminal to execute commands and then click Check my progress to verify your work.
Challenge scenario
You're the cloud architect for a cybersecurity firm. One of your client's virtual machines (VM) in a Google Cloud VPC network (client-vpc) has been compromised by a sophisticated attacker. The attacker is attempting to pivot laterally to other VMs within the network. Your task is to:
- Isolate the compromised VM: Immediately isolate the VM (compromised-vm) from the rest of the client-vpc network by denying the traffic to prevent further lateral movement by removing all ingress access in the existing firewall rule called
critical-fw-rule.
Click Check my progress to verify the objective.
Update the firewall rule.
- Maintain Limited Access: Allow SSH access to the compromised-vm from a specific bastion host (bastion-host) so that your incident response team can investigate the attack. Create this as a new firewall rule called
allow-ssh-from-bastion.
Click Check my progress to verify the objective.
Create the firewall rule.
- Log and Monitor: Enable
VPC flow logsfor the subnetmy-subnetto capture all network traffic to and from the isolated VM for further analysis.
Click Check my progress to verify the objective.
Enable VPC flow logs for the subnet.
Solution of Lab
curl -LO raw.githubusercontent.com/ePlus-DEV/storage/refs/heads/main/labs/respond-to-a-security-incident-solution/lab.sh
source lab.sh
Script Alternative
gcloud compute firewall-rules delete critical-fw-rule --quiet 2>/dev/null; gcloud compute firewall-rules create critical-fw-rule --network=client-vpc --direction=INGRESS --priority=1000 --action=DENY --rules=tcp:80,tcp:22 --target-tags=compromised-vm --enable-logging
gcloud compute firewall-rules delete allow-ssh-from-bastion --quiet 2>/dev/null; gcloud compute firewall-rules create allow-ssh-from-bastion --network=client-vpc --action allow --direction=ingress --rules tcp:22 --source-ranges=\((gcloud compute instances describe bastion-host --zone=\)(gcloud compute instances list --filter="name=bastion-host" --format="get(zone)") --format="get(networkInterfaces[0].accessConfigs[0].natIP)") --target-tags=compromised-vm
gcloud compute networks subnets update my-subnet --region=$(gcloud compute networks subnets list --filter="name=my-subnet" --format="get(region)") --enable-flow-logs